Identity Access Management: Letting the Right One In
As businesses expand their digital presence and embrace hybrid work models, the need for robust Identity Access Management (IAM) solutions has become paramount. At Altiatech, we understand the complexities of IAM and offer tailored solutions to ensure you're always "letting the right one in."

Understanding IAM: More Than Just a Buzzword
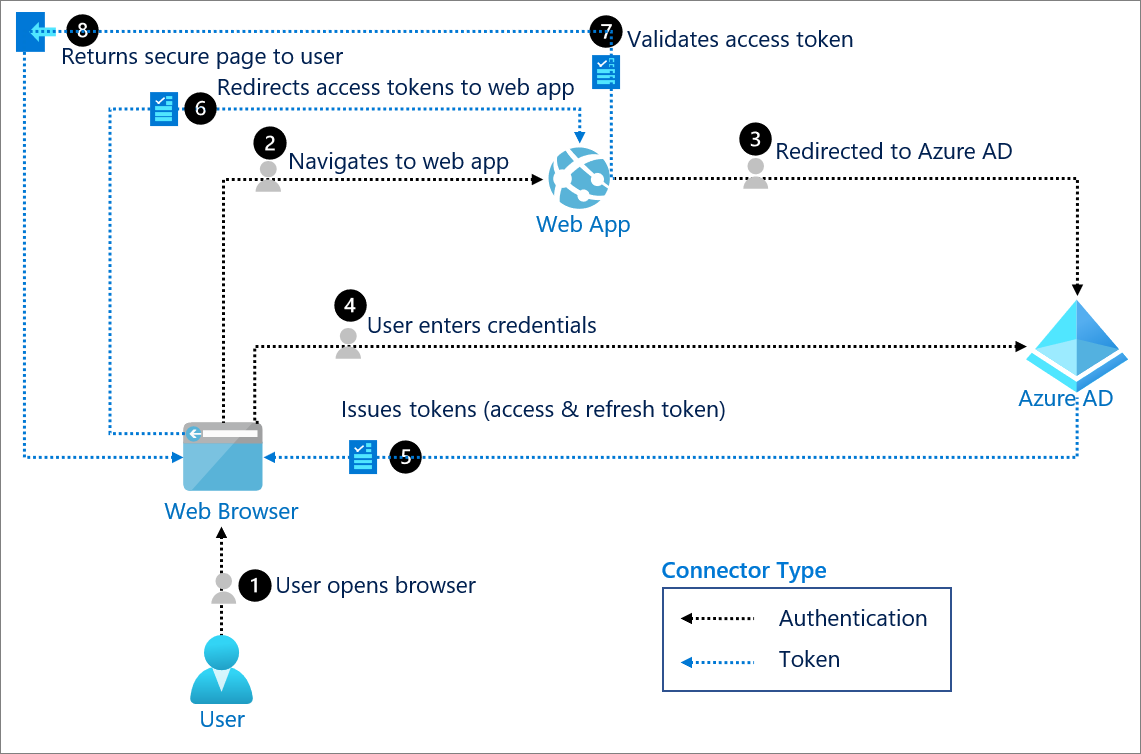
Gartner defines IAM as "a fundamental and critical cybersecurity capability, to ensure the right identities have the right access to the right resources at the right time for the right reasons." At Altiatech, we've distilled this concept into a simple yet powerful phrase: "Let the Right One In."
This folklorish saying reminds us that just as vampires can't enter a house unless invited, cybercriminals shouldn't be able to access your digital estate without proper authorisation. Unfortunately, many successful cyberattacks occur because the bad actors are inadvertently "let in" due to inadequate IAM practices.
The IAM Challenge: Balancing Access and Security
Organisations face a complex challenge: providing frictionless access to their digital resources for employees, customers, suppliers, and even IoT devices, whilst simultaneously maintaining robust security measures. This delicate balance is at the heart of the IAM problem space.
It's crucial to understand that IAM isn't a challenge you can solve by simply adding more software or hiring more staff. An effective and sustainable IAM solution requires careful design, implementation, and ongoing support from subject matter experts.
Why Your IAM Solution Can't Fail
The consequences of a compromised IAM system can be severe:
- Operational disruptions: From reduced manufacturing capacity to power cuts and healthcare service interruptions.
- Financial losses: Including theft, regulatory fines, and customer churn due to data breaches.
- Reputational damage: Loss of customer confidence and brand trustworthiness.
Common IAM Challenges and How Altiatech Can Help
Many organisations struggle with various aspects of IAM implementation:
- Building a compelling business case
- Lack of in-house expertise
- Governance issues and departmental conflicts
- Resistance to change
- Difficulty in managing identity authority
- High delivery complexity leading to project overruns
- Balancing user experience with security
- Selecting the right technology stack
- Keeping up with disruptive digital technologies
- Ensuring regulatory compliance
At Altiatech, we've developed a comprehensive approach to address these challenges and help organisations implement robust IAM solutions.
The Altiatech Approach: DART
Our IAM solution deployment follows the DART process:
- Discovery: We analyse your IAM-related activities, business vision, and governance needs.
- Assessment: We evaluate your current identity processes and systems, providing a gap analysis.
- Recommend: We design solutions and create a roadmap to achieve your desired operating model.
- Transform: We implement the IAM solution, covering Access Management, Governance, Provisioning, and Privilege Access Management.
Tailored Solutions for Your Business
Every organisation is unique, and so are its IAM needs. Our goal at Altiatech is to help your business become cybersecure by implementing a best-practice IAM solution tailored to your specific requirements. Whether you need help with Single Sign-On (SSO), Multi-Factor Authentication (MFA), or a comprehensive IAM strategy, we have the expertise to guide you.
Take the Next Step in Your IAM Journey
Are you ready to enhance your cybersecurity posture and ensure you're only "letting the right one in"?
Contact Altiatech today for an IAM Solution Maturity Assessment. Our experts can help you navigate the complex world of Identity Access Management and implement a solution that keeps your digital assets secure whilst enabling your business to thrive.
Don't leave your digital front door unguarded. Let Altiatech help you build a robust IAM strategy that protects your business today and scales for tomorrow's challenges.
Phone:
0330 332 5482
Email: cyber@altia.tech